Blog
Cloud security lessons, Zero Trust insights, and the occasional cat joke.
From Authorization to Action: Operationalizing CISA's Microsoft Cloud Logs Playbook in Sentinel
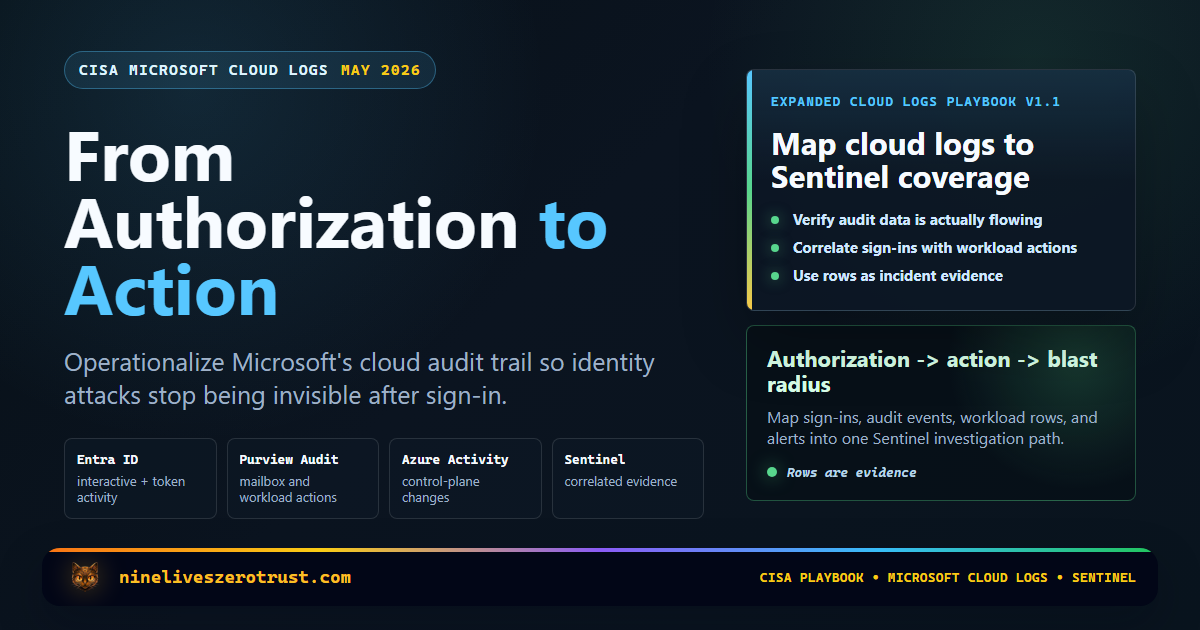
CISA originally released the Microsoft Expanded Cloud Logs Implementation Playbook on January 15, 2025. The CISA resource page shown below also has a May 1, 2026 revision date, and the May 2026 DOCX I reviewed is marked as version 1.1 with general …
Copy Fail in the Cloud: A Defender, Sentinel, and AKS Response Guide for CVE-2026-31431
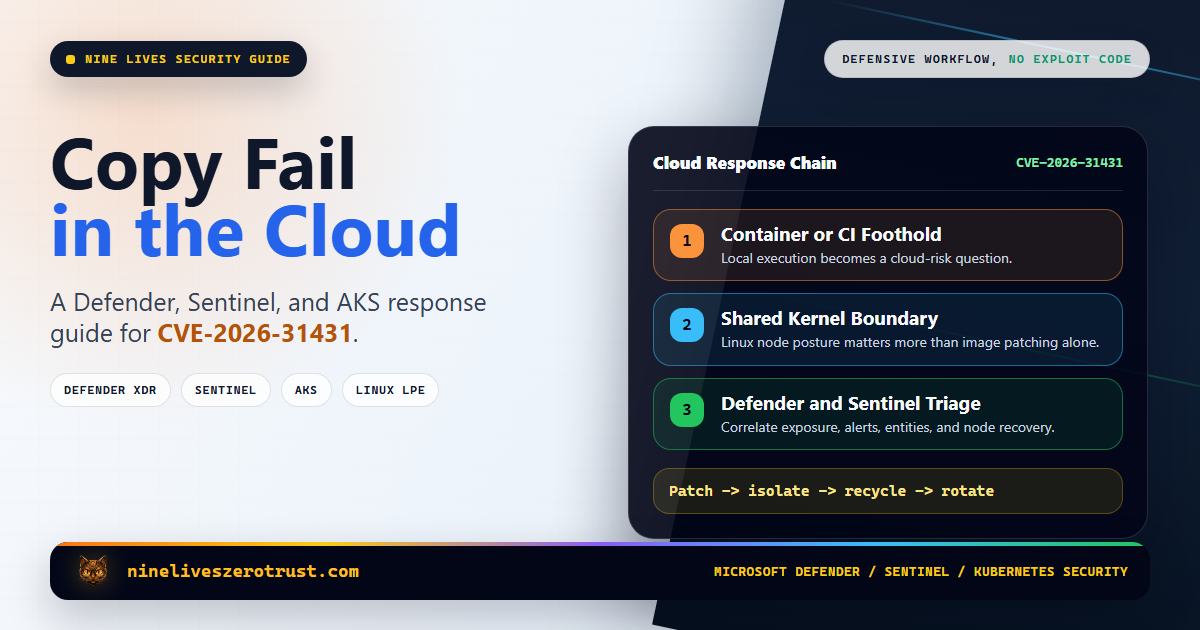
A Linux local privilege escalation bug is easy to dismiss if you only think in traditional server terms. An attacker already needs local access, so how bad can it be? In cloud environments, that assumption breaks fast. A compromised container, a …
Block Device Code Phishing in Entra Without Breaking Legit Workflows

Device code phishing is nasty because the user does not hand over a password. They hand over a session. The lure sends the victim to a legitimate Microsoft device sign-in page. The victim enters a short code. Entra ID issues tokens to the attacker’s …
Agent 365 Launch Playbook: I Tested the Defender Response for AI Agent Attacks
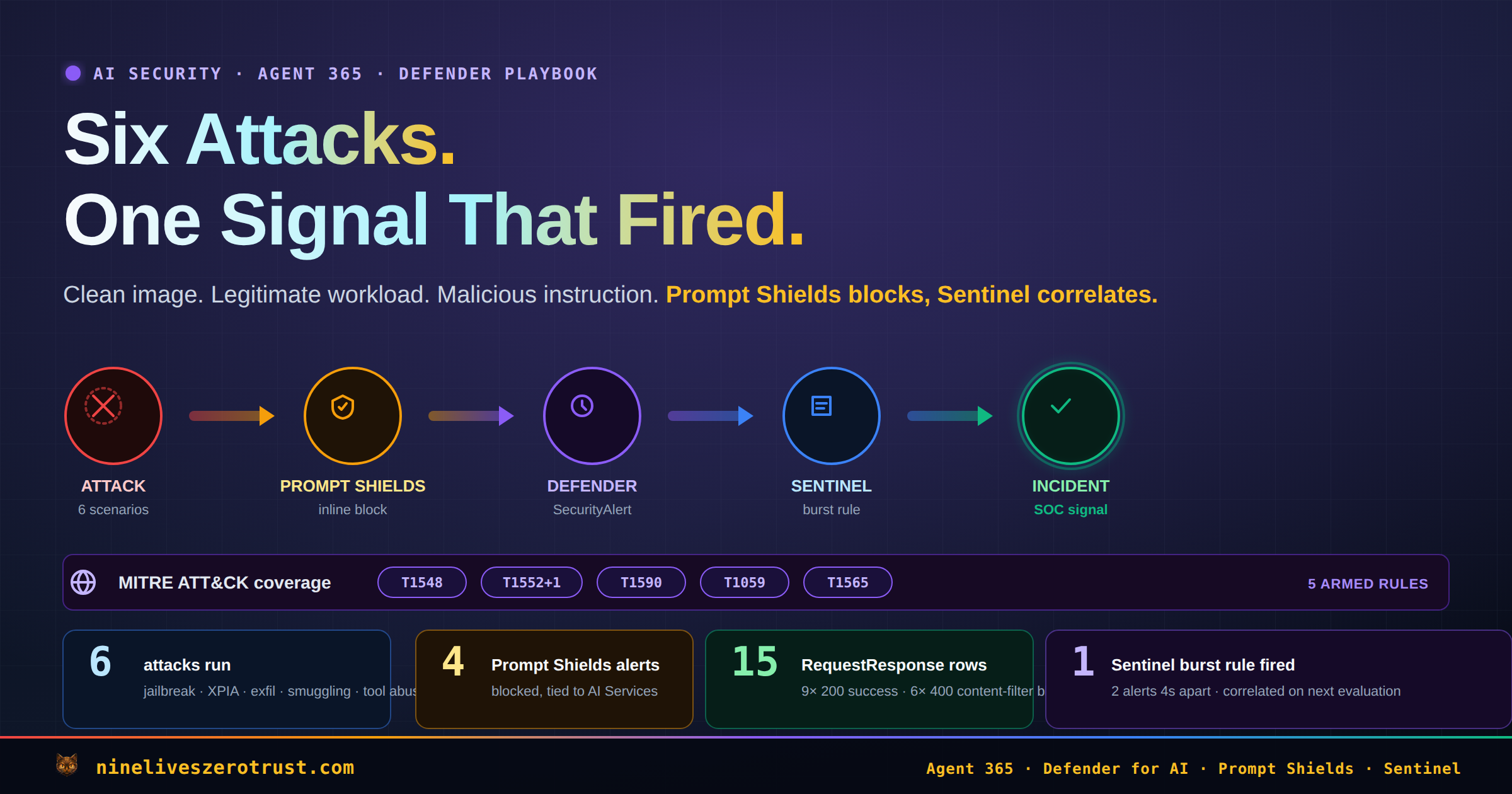
Microsoft announced that Agent 365 would become generally available on May 1, 2026. Most launch-week posts explain what it is. I wanted to answer a different question: What does an AI agent attack look like in a real Microsoft defender stack as Agent …
Scan Every Blob, Trace Every Read: Defender for Storage + Sentinel
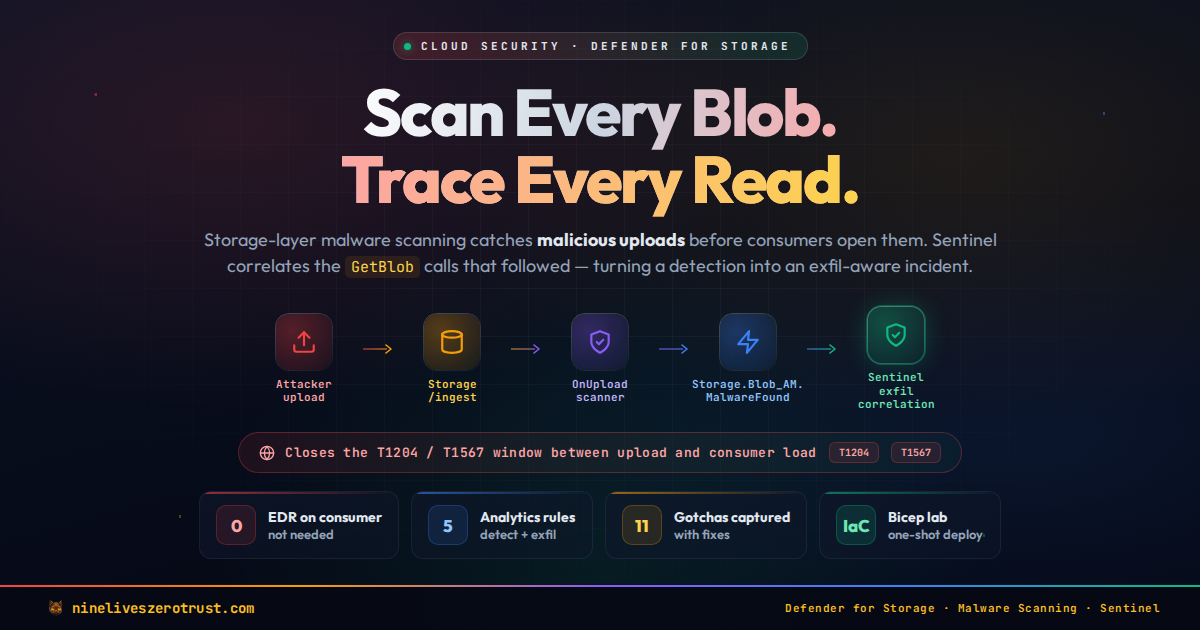
Storage is where malware waits. A blob uploaded to ingest/ by a pipeline step, a partner’s SFTP connector, or a misconfigured Logic App sits quietly until something downstream opens it — a Data Factory copy, a Function app, a Synapse notebook, a …
Detecting Infostealer Session Hijacking with Microsoft Sentinel

Nearly 70% of incidents in the Americas now begin with stolen or misused accounts. Infostealers are the engine behind that number – families like Lumma, RedLine, and Vidar export browser cookies and session tokens directly from the victim’s machine, …
Investigate Hidden Privilege Paths with Microsoft Sentinel Data Federation and Custom Graphs
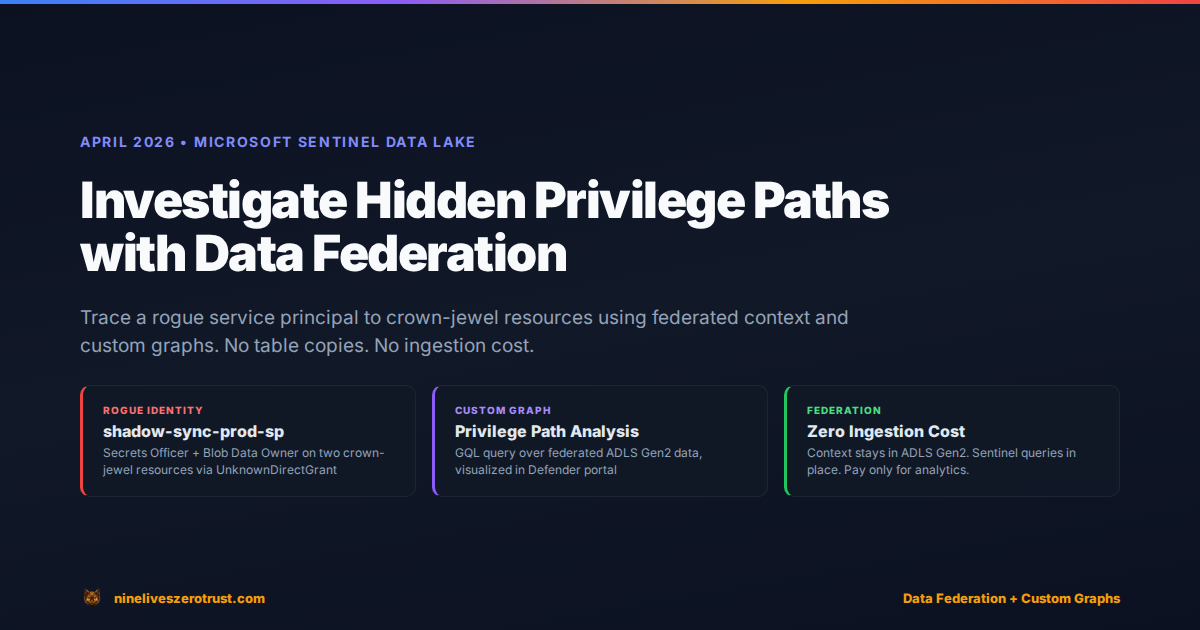
After a compromised service principal incident, the first triage question is always the same: “What else can this identity reach?” The answer usually lives outside Sentinel, buried in entitlement exports, RBAC snapshots, or asset inventories that …
Block Prompt Injection at the Network Layer with Entra Internet Access Prompt Shield
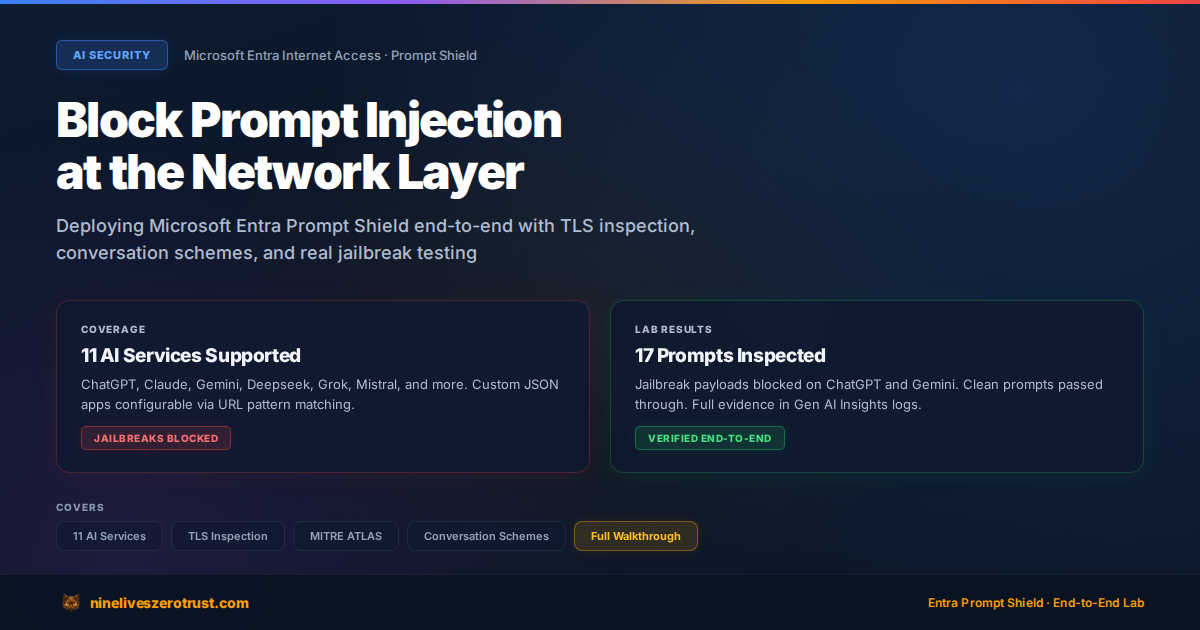
A while back I built an LLM Firewall with AWS Lambda, a proxy that sits between users and the model to catch prompt injection. It worked, but it meant writing custom code for every app and having zero visibility into AI services I didn’t own. That’s …
Building Custom Sentinel Connectors in One Click with CCF Push
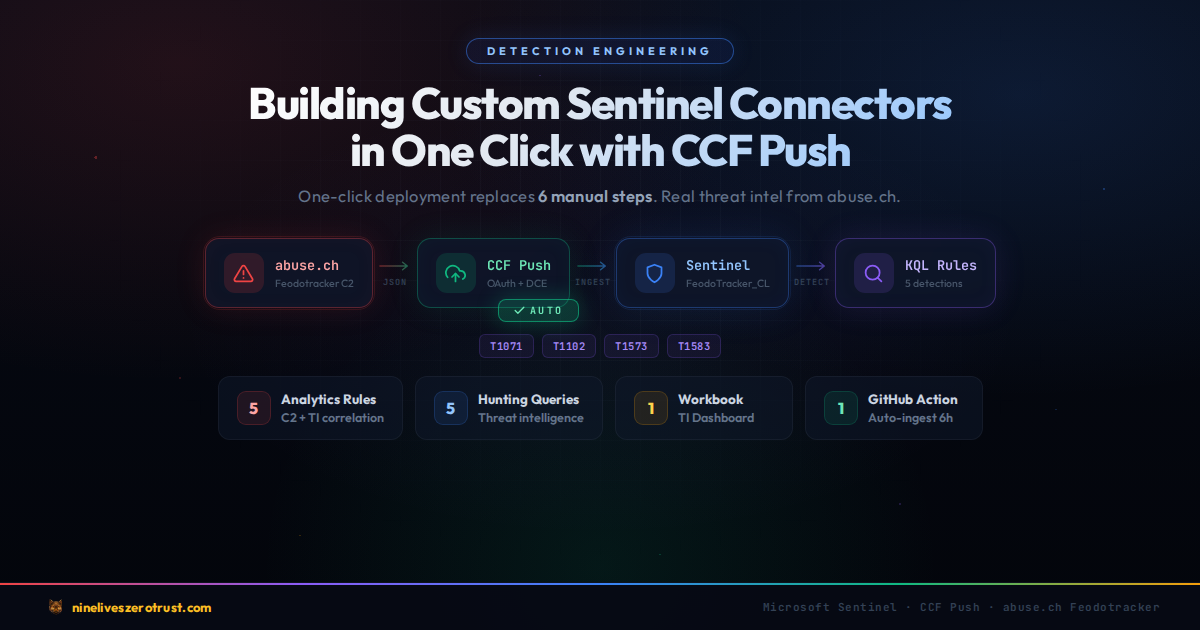
Getting custom data into Microsoft Sentinel has traditionally required a lot of moving parts. You need a Data Collection Endpoint, a Data Collection Rule, an Entra app registration with a client secret, RBAC role assignments, a custom table …
AKS Runtime Security: Binary Drift, Anti-Malware & Gated Deployment with Defender for Cloud

In December, I published a post on securing the container supply chain — SBOM generation, image signing, and build provenance with GitHub Actions. That covered build-time security: making sure the image you ship is the image you built. But what …

