Entra-Id
Lessons from the field. Always landing on my feet.
Block Device Code Phishing in Entra Without Breaking Legit Workflows

Device code phishing is nasty because the user does not hand over a password. They hand over a session. The lure sends the victim to a legitimate Microsoft device sign-in page. The victim enters a short code. Entra ID issues tokens to the attacker’s …
Detecting Infostealer Session Hijacking with Microsoft Sentinel

Nearly 70% of incidents in the Americas now begin with stolen or misused accounts. Infostealers are the engine behind that number – families like Lumma, RedLine, and Vidar export browser cookies and session tokens directly from the victim’s machine, …
Detecting OAuth Redirect Abuse with Microsoft Sentinel and Entra ID

On March 2, 2026, Microsoft published an advisory on OAuth redirection abuse enabling phishing and malware delivery. Microsoft described phishing-led campaigns where attackers register OAuth apps with attacker-controlled redirect URIs, then send …
The February 2026 Microsoft Sentinel Drop: UEBA Essentials, Copilot Connector, and 9 New GA Connectors
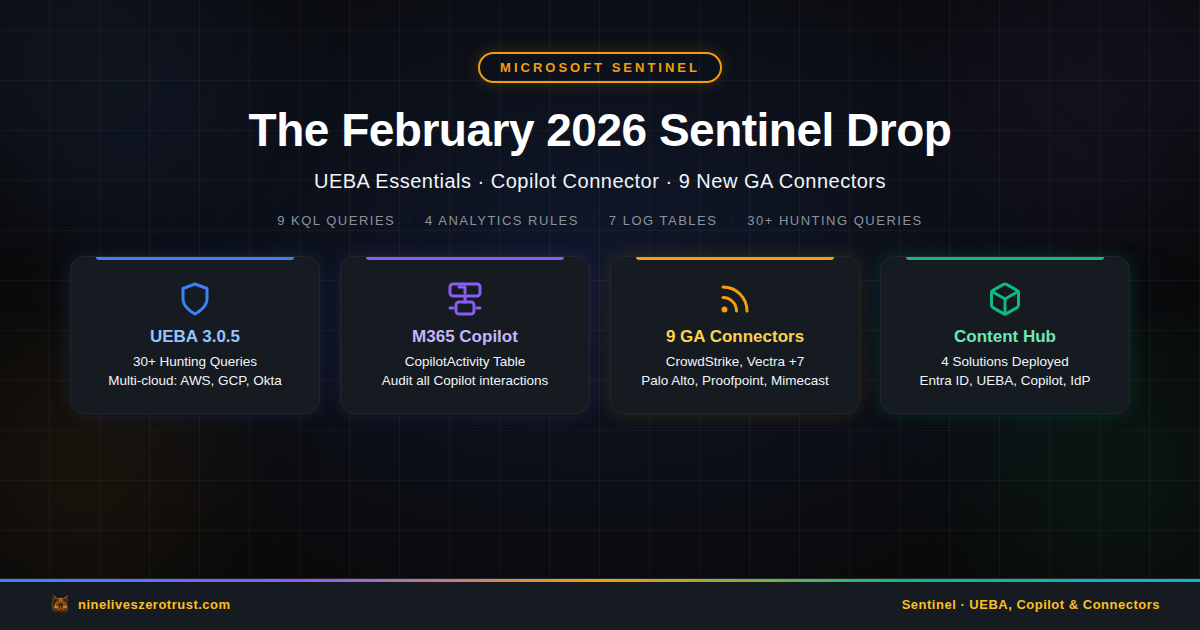
February 2026 brought one of the more substantial Sentinel drops in recent memory. UEBA Essentials hit v3.0.6 with a refined workbook and more than 30 hunting queries (including multi-cloud detections shipped in earlier releases), the M365 Copilot …
March 2026 Entra ID Changes: Passkey Auto-Enablement and Conditional Access Enforcement

Microsoft is shipping two Entra ID changes in March 2026 that will change how your users authenticate. Neither change requires administrator action to take effect, and that is precisely the risk. If you do not act before the deadlines, Microsoft …
Just-In-Time Access for AI Agents: Building a ZSP Gateway in Azure
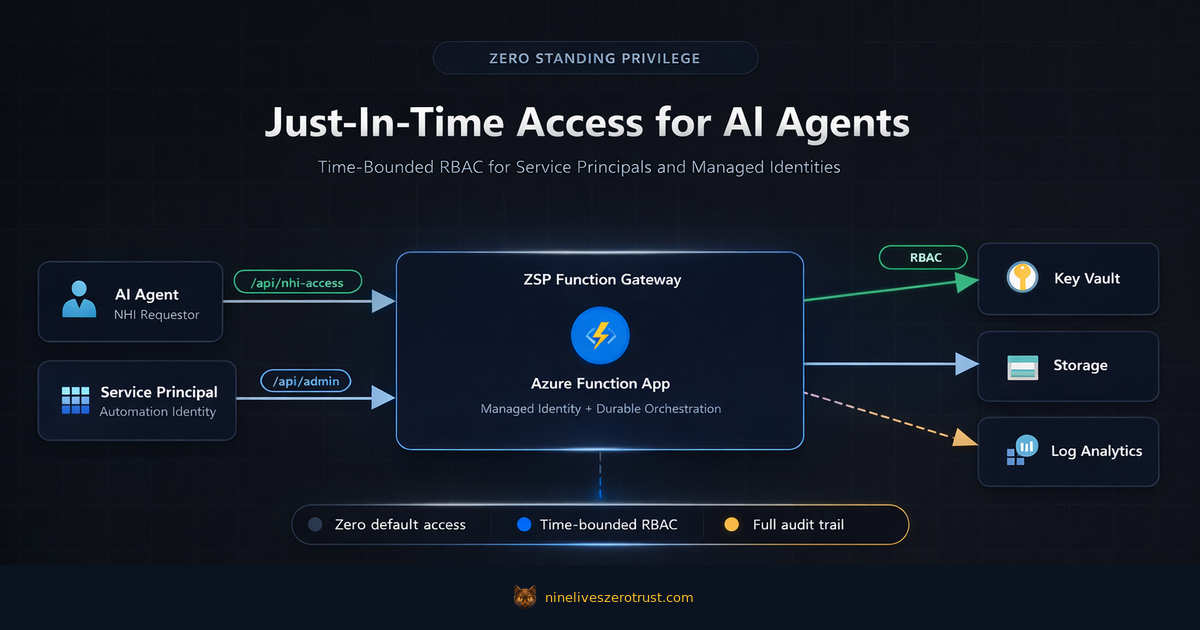
AI coding assistants need Contributor access to deploy infrastructure. Backup automation needs Key Vault secrets at 2 AM. Security scanners need Reader access on a schedule. The easy answer is standing permissions-give each service principal what it …

