Mitre-Attack
Lessons from the field. Always landing on my feet.
Scan Every Blob, Trace Every Read: Defender for Storage + Sentinel
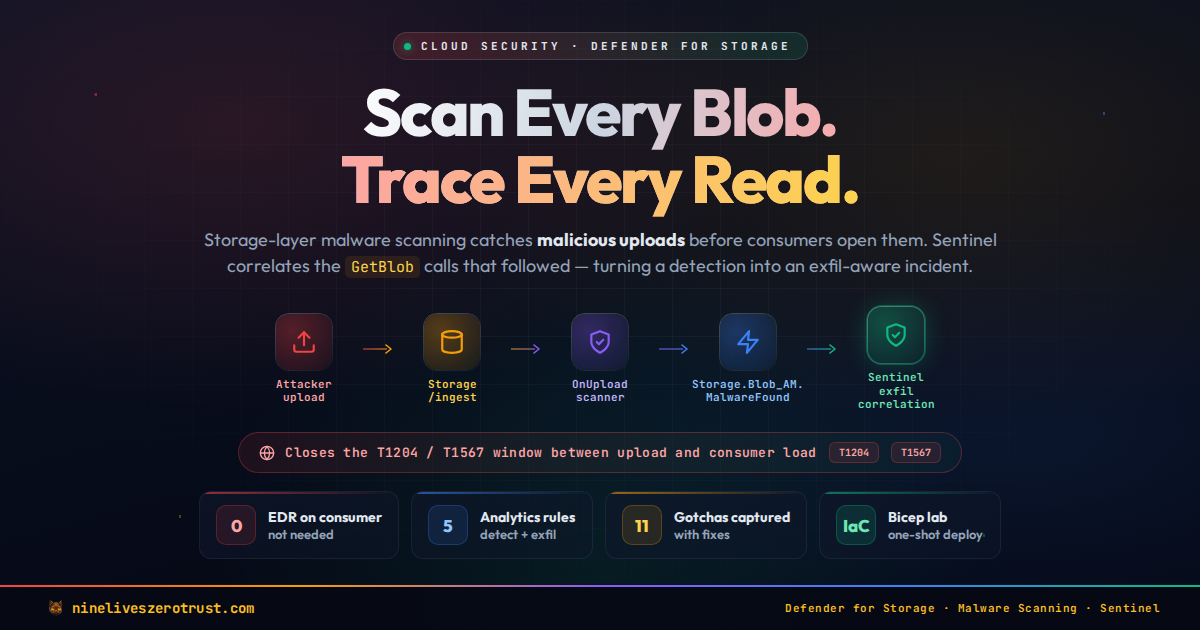
Storage is where malware waits. A blob uploaded to ingest/ by a pipeline step, a partner’s SFTP connector, or a misconfigured Logic App sits quietly until something downstream opens it — a Data Factory copy, a Function app, a Synapse notebook, a …
Detecting Infostealer Session Hijacking with Microsoft Sentinel

Nearly 70% of incidents in the Americas now begin with stolen or misused accounts. Infostealers are the engine behind that number – families like Lumma, RedLine, and Vidar export browser cookies and session tokens directly from the victim’s machine, …
Building Custom Sentinel Connectors in One Click with CCF Push
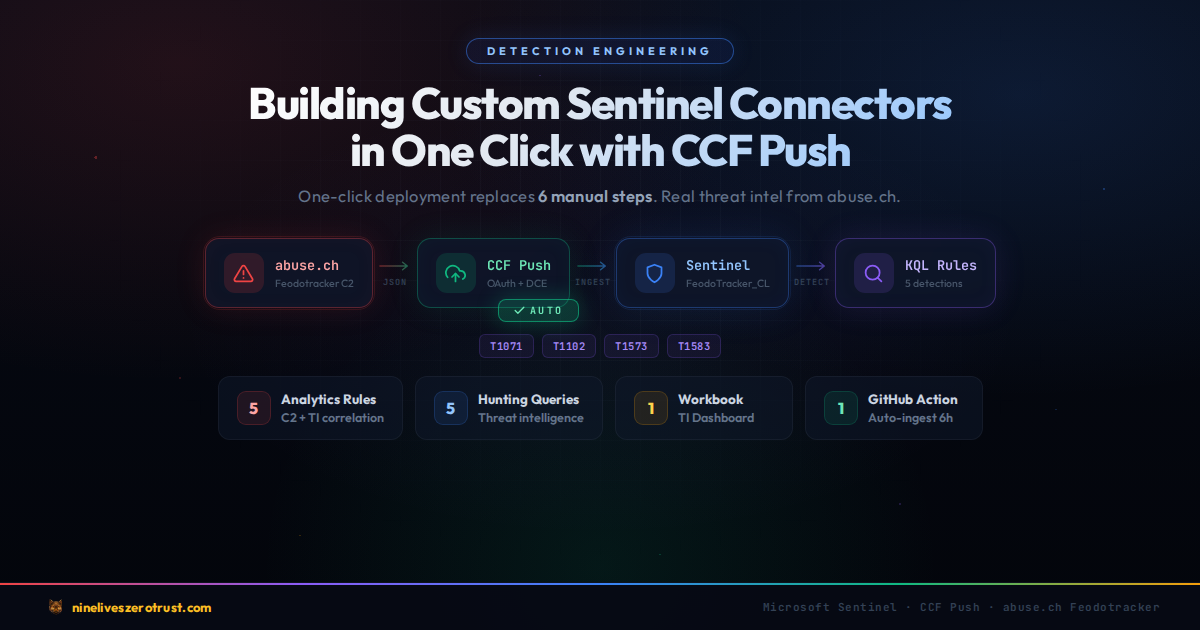
Getting custom data into Microsoft Sentinel has traditionally required a lot of moving parts. You need a Data Collection Endpoint, a Data Collection Rule, an Entra app registration with a client secret, RBAC role assignments, a custom table …
AKS Runtime Security: Binary Drift, Anti-Malware & Gated Deployment with Defender for Cloud

In December, I published a post on securing the container supply chain — SBOM generation, image signing, and build provenance with GitHub Actions. That covered build-time security: making sure the image you ship is the image you built. But what …
Detecting OAuth Redirect Abuse with Microsoft Sentinel and Entra ID

On March 2, 2026, Microsoft published an advisory on OAuth redirection abuse enabling phishing and malware delivery. Microsoft described phishing-led campaigns where attackers register OAuth apps with attacker-controlled redirect URIs, then send …

